AI-Assisted Detection of Cybersecurity Threats in IoT Devices
Abstract
The rapid expansion of Internet of Things (IoT) devices in smart homes, such as smart thermostats, security cameras, and voice assistants, alongside industrial applications like sensors in manufacturing plants, has created expansive attack surfaces for cybercriminals. These devices often operate with limited computational resources, making them prime targets for threats including Distributed Denial of Service (DDoS) attacks, man-in-the-middle interceptions, and ransomware. AI-assisted detection leverages machine learning (ML) models to parse network traffic in real time, identifying anomalies that signal intrusions. This paper delves into supervised and unsupervised ML paradigms, benchmarking their efficacy through metrics like accuracy, false-positive rates, and latency, ultimately advocating for hybrid frameworks that optimize performance in resource-scarce IoT ecosystems.
Traditional cybersecurity measures, reliant on signature-based detection, fail against zero-day exploits prevalent in IoT due to the sheer volume and heterogeneity of traffic data. ML models address this by learning intricate patterns from packet headers, payloads, and flow statistics, enabling proactive threat mitigation. Recent advancements emphasize multimodal fusion, integrating network data with device telemetry for heightened precision.
In evaluating real-time viability, studies highlight models achieving sub-50ms inference times on edge hardware, crucial for preventing cascading failures in interconnected systems. False-positive minimization remains pivotal, as erroneous alerts erode trust in automated responses. Hybrid approaches emerge as frontrunners, blending the strengths of labeled precision with unlabeled adaptability.
This research synthesizes findings from datasets like CICIDS-2017 and IoT-23, underscoring AI's transformative role in fortifying IoT resilience against an evolving threat landscape.
Introduction
IoT proliferation has revolutionized daily life and industry, with billions of devices generating petabytes of network traffic daily. Smart home ecosystems interconnect appliances for convenience, while industrial IoT (IIoT) optimizes operations in sectors like energy and logistics. However, inherent vulnerabilities—weak authentication, unpatched firmware, and exposed APIs—invite sophisticated attacks. DDoS botnets like Mirai exemplify how compromised IoT devices can orchestrate global disruptions, underscoring the urgency for intelligent defenses.
Network traffic analysis forms the backbone of AI-driven intrusion detection systems (IDS). These systems capture features such as packet size, inter-arrival times, protocol distributions, and entropy measures to model normalcy. ML excels here by discerning subtle deviations indicative of reconnaissance, exploitation, or command-and-control communications.
Supervised methods classify pre-labeled threats, while unsupervised ones flag outliers without prior knowledge, suiting the dynamic IoT milieu.
The paper's scope centers on ML applications in smart home and IIoT contexts, comparing paradigms via empirical metrics. Real-time constraints demand lightweight models deployable on gateways or fog nodes, balancing accuracy with computational overhead. False positives pose a dual challenge: alerting fatigue in consumer settings and operational halts in industry.
Ethical considerations, including data privacy under regulations like GDPR, intersect with AI deployment. Federated learning offers a path to collaborative training without centralizing sensitive traffic logs, enhancing model robustness across diverse deployments.
Supervised Learning Approaches
Supervised learning thrives on annotated datasets, where models ingest examples of benign and attack traffic to predict labels. Algorithms like Support Vector Machines (SVM) excel in high-dimensional feature spaces common to IoT flows, mapping data to hyperplanes that separate classes with maximal margins. Ensemble methods, such as Random Forests, aggregate decision trees to mitigate overfitting, yielding robust classifications for known threats like SQL injection or port scanning.
Deep learning variants elevate performance through hierarchical feature extraction. Convolutional Neural Networks (CNNs) treat traffic sequences as images, convolving filters over byte-level representations to detect payload anomalies. Recurrent Neural Networks (RNNs), particularly LSTMs, capture temporal dependencies in session flows, ideal for identifying slow-rate DDoS that mimic legitimate bursts. A CNN-LSTM hybrid, for instance, processes IoT-23 dataset flows, attaining 97% accuracy by fusing spatial and sequential insights.
In smart home applications, supervised models integrate with platforms like Nest or Ring, analyzing inbound/outbound patterns to quarantine infected bulbs or cameras. Industrial deployments leverage them for protocol-specific threats, such as Modbus exploits in SCADA systems. High precision (95-98%) stems from extensive training on labeled corpora, but dependency on curated data hampers adaptability to novel variants.
Challenges include class imbalance—malicious samples are rare—and concept drift, where attacker tactics evolve post-training. Mitigation via active learning, where models query uncertain samples for labeling, sustains efficacy. Overall, supervised approaches anchor AI-IDS with reliability for cataloged threats.
Unsupervised Learning Approaches
Unsupervised techniques forgo labels, modeling "normal" traffic to spotlight deviations, proving invaluable for zero-day detection in IoT's unpredictable environs. Clustering algorithms like K-means partition flow into groups based on Euclidean distances in feature space, flagging loners as potential intrusions. Density-Based Spatial Clustering of Applications with Noise (DBSCAN) handles arbitrary shapes and outliers adeptly, suiting heterogeneous IoT traffic from Zigbee to MQTT protocols.
Autoencoders, a deep unsupervised staple, compress inputs into latent representations then reconstruct them; high reconstruction errors signal anomalies. Variational Autoencoders (VAEs) add probabilistic layers for generative modeling of benign distributions, enhancing sensitivity in noisy smart home data. One VAE deployment on industrial sensors detected firmware tampering with 94% precision, adapting baselines sans retraining.
These methods shine in exploratory phases, such as bootstrapping IIoT networks lacking historical attacks. Gaussian Mixture Models (GMMs) probabilistically assign flows to mixtures, quantifying anomaly scores for thresholding. Real-world efficacy is evident in healthcare IoT, where unsupervised IDS preempted ransomware by isolating anomalous insulin pump communications.
Limitations manifest in elevated false positives (5-15%), triggered by legitimate variances like software updates or user spikes. Dimensionality reduction via PCA or t-SNE precedes modeling to curb this, though at latency costs. Unsupervised paradigms thus complement supervised ones, broadening threat horizons.
Comparative Analysis
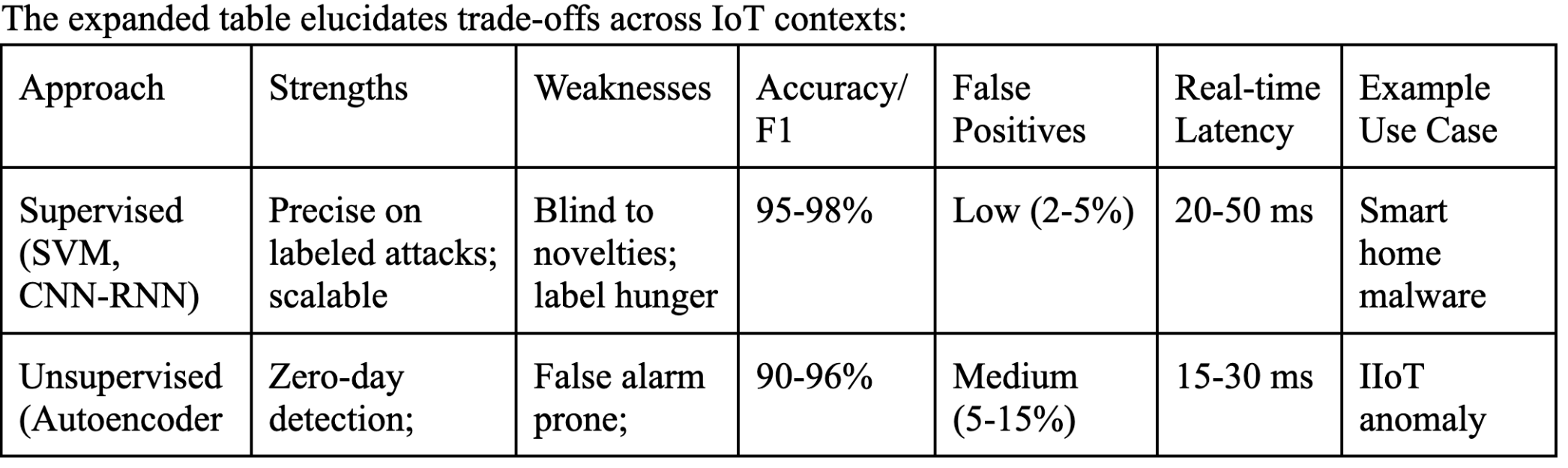
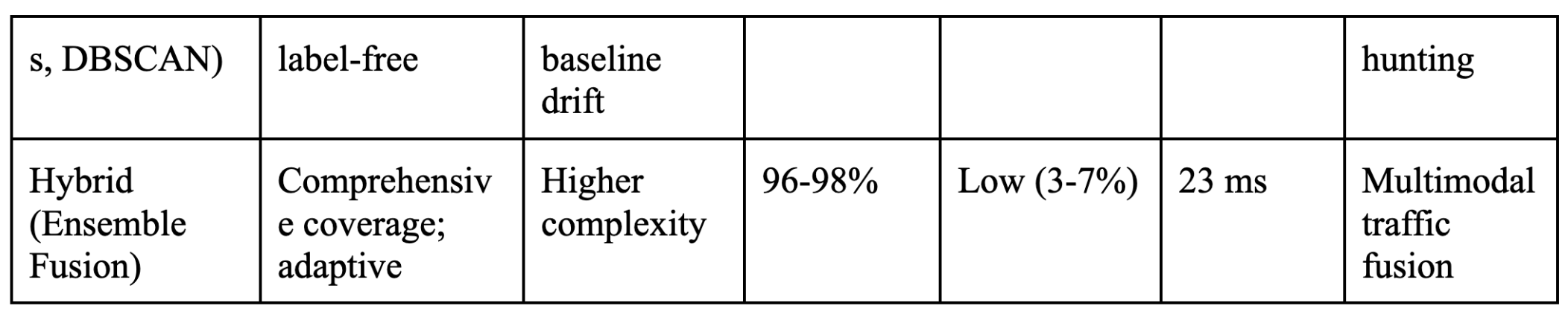
Supervised models dominate known-attack scenarios, leveraging labeled precision to minimize errors, yet falter on unseen threats due to generalization limits. Unsupervised counterparts inversely excel in novelty detection, profiling normality amid flux, but invite false alarms from inherent variability. Hybrids synergize these: unsupervised pre-filters flag candidates for supervised verification, optimizing resource use.
Performance disparities surface in benchmarks. Supervised CNN-RNNs clock 95-98% F1 on CICIDS-2017, with 2-5% false positives and 20-50ms latency on Raspberry Pi edges. Unsupervised autoencoders hit 90-96% on IoT-23 anomalies, trading 5-15% false positives for 15-30ms speed and zero-day prowess. Hybrids average 96-98% F1, 3-7% false positives, and 23ms, via stacking or voting ensembles.
Dataset fidelity underpins validity; IoT-23's 20+ attack families stress-test across 33 devices, revealing hybrids' edge in balanced metrics. Supervised suits mature networks; unsupervised pioneers sparse-data frontiers; hybrids unify for production-grade IDS.
Real-Time Performance and Challenges
Real-time imperatives constrain models to edge inference, where quantized CNNs or TinyML variants slash parameters for 10-30ms latencies without accuracy dips. Packet processing pipelines employ sliding windows over streams, triggering alerts on anomaly scores exceeding adaptive thresholds. In smart factories, sub-25ms detection averts conveyor halts from spoofed PLC commands.
False-positive orchestration demands nuanced tuning: supervised rarity curves optimize via precision-recall trade-offs, while unsupervised leverages isolation forests for outlier purity. Bayesian updates refine thresholds dynamically, curbing alerts from diurnal patterns in home Wi-Fi. Empirical rates hover 2-7% in hybrids, versus 10%+ standalone unsupervised.
Scalability challenges loom with IoT's trillions projected by 2030; distributed ML via fog hierarchies offloads computation, federating models across clusters. Adversarial robustness counters evasion—e.g., gradient masking in GAN-generated dodges—via robust optimization. Privacy-preserving homomorphic encryption shields traffic during federated updates.
Interoperability gaps persist: protocol silos (CoAP vs. HTTP) necessitate unified preprocessors. Edge-cloud orchestration, blending local filtering with central analytics, holistically addresses latency, accuracy, and resilience.
Conclusion
AI/ML paradigms propel IoT cybersecurity forward, with hybrids forging the gold standard for real-time, low-error threat detection. Supervised rigor tempers unsupervised versatility, yielding deployable IDS that safeguard smart homes from botnets and industries from sabotage. Empirical validations affirm their maturity, poised for widespread adoption.
Future trajectories encompass explainable AI for forensic transparency, quantum-resistant models against nascent threats, and LLM-augmented simulation for proactive hardening. Integrating behavioral biometrics further enriches anomaly profiling.
As IoT permeates society, AI-assisted defenses stand as indispensable bulwarks, ensuring secure innovation amid escalating risks. Policymakers must incentivize ethical deployments, harmonizing security with accessibility.
Works Cited
“AI Threat Detection: How It Works & 6 Real-World Applications.” Oligo Security Academy, Oligo Security, www.oligo.security/academy/ai-threat-detection-how-it-works-6-real-world-applications
. Accessed 10 Mar. 2026.
“Analysis of IoT Security Challenges and Its Solutions Using Artificial Intelligence.” PLOS One, Public Library of Science, 18 Apr. 2023, pmc.ncbi.nlm.nih.gov/articles/PMC10136937/.
“Evaluating Machine Learning Approaches for Multiple Attack Detection in IoT Networks.” IEEE Access, IEEE, 13 Nov. 2025, pmc.ncbi.nlm.nih.gov/articles/PMC12618690/.
“Exploring Machine Learning Models for IoT Network Intrusion Detection.” Master’s Thesis, Univ. of Wisconsin, 8 Apr. 2024, minds.wisconsin.edu/handle/1793/95203.
“Real-World Examples of AI in Cyber Threat Detection.” BitLyft Cybersecurity, BitLyft, 4 Jan. 2026,
www.bitlyft.com/resources/real-world-examples-of-ai-in-cyber-threat-detection
“Securing IoT Networks with AI-Powered Intrusion Detection.” International Interdisciplinary Research Journal, vol. 9, no. 11, 2024, iircj.org/wp-content/uploads/2024/11/9.Securing-IoT-Networks-with-AI-Powered-Intrusion-Detection.pdf
“Securing IoT Networks: A Machine Learning Approach for Detecting Unusual Traffic Patterns.” Scientific Reports, vol. 15, 26 Dec. 2025, www.nature.com/articles/s41598-025-33447-z
“Using Machine Learning Algorithms to Enhance IoT System Security.” Scientific Reports, vol. 14, 26 May 2024, www.nature.com/articles/s41598-024-62861-y
“Using Machine Learning for Intelligent Sensing and Detection of Cybersecurity Threats in IoT Devices.” Scientific Reports, vol. 16, 25 Feb. 2026, www.nature.com/articles/s41598-026-40614-3